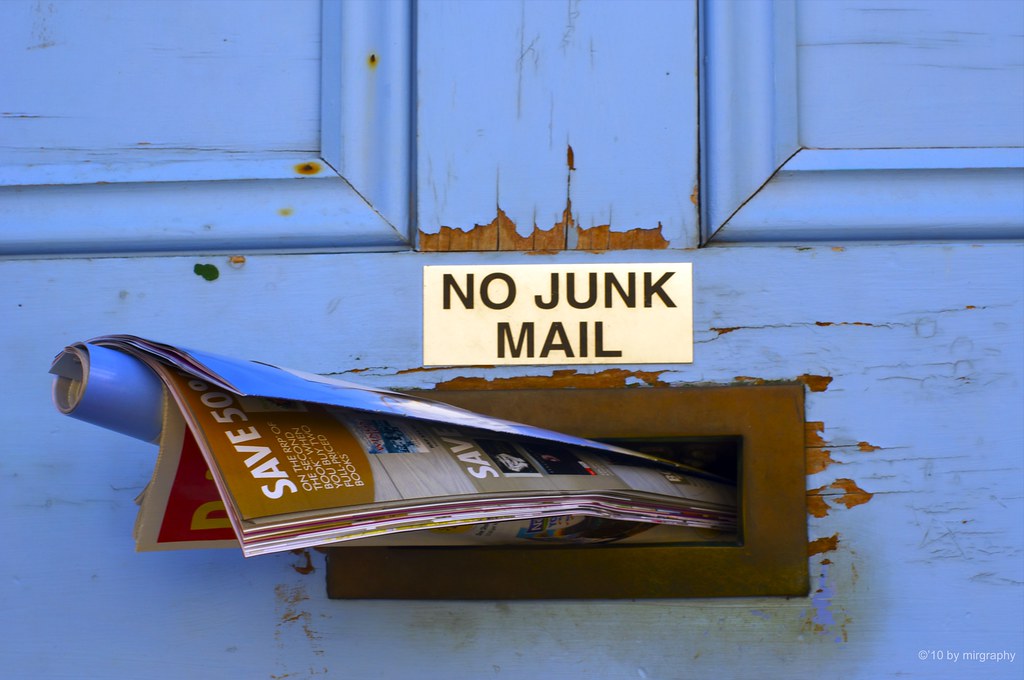
As popularly quoted, nothing in this world can be said to be certain except death and taxes. But if you were to survey people today to ask what else should be added to that list, there’s a good chance that email spam would be a worthy contender. It’s almost a certainty that you’ll have at least one piece of spam in your inbox when checking your email on any given day. So, here’s some background on spam followed up by our recommendation on how to solve your spam problem.
One reason why just about anyone will tell you that their mailbox receives tons of spam is because of how ambiguous of a term “spam” really is. There are many factors that can influence the thoughts of a person when making a quick decision about whether the email that they’re looking at is legitimate or junk. Unfortunately for all of us though, computer systems that automatically filter your email aren’t as subjective and instead rely on specific characteristics to make a determination. This can result in a difference of opinion between the user and the computer.
You may not always agree with your email’s spam filtering decisions. But there are a few things that you can do to help identify what truly is considered spam and work together with your computer to help fight against it. So what exactly is “spam email” and how can you keep it under control? Read ahead for some tips and tricks.
What is spam? Like I mentioned above, the answer to that can vary based on who you ask. But technically speaking, email spam is mail that is unsolicited and often sent out to recipients in bulk. Its content is of an advertising or malicious nature intended to garner some sort of response. That hopeful response isn’t necessarily always a reply though as it can be click tracking, read receipts, or something really bad such as a phishing attempt.
There’s also certain emails that are considered spam to you but legitimate to your computer. For example, news and offers from mailing lists that you agreed to. When doing online shopping, it’s likely that part of the checkout process contained a checkmark next to a statement such as “Keep me up to date on exclusive offers from us and our partners”. When you agree to those terms, you are authorizing that company to use your email address in its marketing campaigns. And as long as they meet common email marketing standards which we’ll cover below, the email will likely be delivered right to your inbox.
Thankfully, there are a few things that you can do with your computer to tag-team against those pesky spam emails. Lets break this down into three email categories:
Legitimate marketing emails
Remember those mailing lists I mentioned above? Just because you agreed to receive them at some point doesn’t mean that you are locked into receiving them forever. Emails that fall into this category are required to comply with the federal CAN-SPAM Act. You can read more about the details of it in this link but the following are the requirements that the sender must abide by.
- Don’t use false or misleading header information.
- Don’t use deceptive subject lines.
- Identify the message as an ad.
- Tell recipients where you’re located.
- Tell recipients how to opt out of receiving future email from you.
- Honor opt-out requests promptly.
- Monitor what others are doing on your behalf.
Number five is critical here. All messages that qualify under this category must include clear instructions on how you can remove yourself from the mailing list. This can commonly be found at the bottom of the message. If you would like to unsubscribe from a mailing list, look for a link at the bottom labeled “Unsubscribe”. If it is not a link, it may contain specific instructions about who to contact.
If the message is from a legitimate business that wants to maintain their anti-spam reputation, they must honor your request.
There is the possibility though that an email that you think is a legitimate marketing email is actually fraudulent or malicious. Because of this, you must still take caution when unsubscribing from marketing emails. The unsubscribe request should never require you to provide any additional information about yourself. If the message requests any personal information such as your address, phone number, or credit card information, do not provide it and categorize it as malicious which I’ll describe below.
Random content spam
In some cases, you may receive spam email from an unknown sender that may be asking a generic question such as “How are you?” or “Are you there?”. While it may seem like its possibly just a mistake at first glance, this type of spam serves a very specific purpose. It is looking for active email addresses. All the sender wants is some sort of acknowledgement that your email address is being used so that it can be added to unsolicited mailers or sold in a database to malicious individuals.
If you have a message like this in your inbox, there are a few things that you should not do.
- Do not reply.
- If asked to send a read receipt, say no.
- If asked to download images or other content, say no.
Instead of those actions, do the following.
- Mark the message as junk so that future emails from that sender automatically get delivered to your spam or junk mail folder. The process to do so can vary based on application and email system so consult your system’s help documentation for instructions.
- Delete the email and empty your recycle bin.
In most cases, these types of emails are few and far between. While seemingly simple, they require more manual effort and tracking for little reward.
Phishing and malware
This is the worst type of spam that you can receive in your mailbox. If an email in this category has made it to your inbox, special care should be given to help keep it under control.
So what constitutes a message falling into this category? The following are some common examples.
- Attachments that you were not anticipating.
- Uncommon requests from a colleague such as being asked to pick up gift cards or make a wire transfer.
- Threatening to harm the recipient for not complying with random demands.
- Being asked to provide or reset your password when the action was not initiated by you through a legitimate website.
- Being asked to click a link and then provide personal information of any kind.
In some email systems, the way to remove these messages from your inbox and block the sender are the same as you would perform for the prior category. However, some email systems such as Microsoft 365 have introduced separate measures to report messages as phishing attempts. This helps prioritize the action taken and allows for more severe automation on the system’s side. You should check your system’s help documentation to see if they recommend a specific way to report phishing and malware.
If you have received a message of this type to your work email address, you should also report it to your company’s I.T. department for further analysis. There may be action that they can take to prevent the same or similar messages from reaching your colleagues. This is especially important if you suspect that you may have fallen for any of the sender’s tactics.
Whether it is helping to keep control of your email or ensuring that your company’s infrastructure is as solid as can be, Diligex can help your business thrive. If you are a Diligex TotalCare client and are ever unsure about the legitimacy of an email message, feel free to let us know and we will be happy to assist with providing an analysis. If you are not currently a Diligex Total Care subscriber, feel free to contact us at https://diligex.com/contact to learn how Diligex can help keep your company’s data safe and secure.
